In a group of six women there are four table tennis players, four post-graduates in Economics, one post-graduate in Commerce and three bank employees. Beena and Priya are among the bank employees while Megha and Garima are unemployed. Priya and Latika are among the table tennis players. Megha, Priya, Garima and Latika are post-graduates in Economics of whom two are bank employees. If Zoya is a post-graduate in Commerce, who among the following is both a table tennis player and a bank employee?
A)
Latika
done
clear
B)
Zoya
done
clear
C)
Megha
done
clear
D)
Garima
done
clear
View Answer play_arrow
If' '+' means 'subtraction', '\[\div \]' means 'addition', '\[\hat{\ }\]' mans 'less than', '-' means 'greater than', '\[\times \]' means 'equal to', '\[<\]' means 'multiplication' and '\[>\]' means 'division', then which of the following is true?
A)
\[9\hat{\ }5+2\div 4>12~~\]
done
clear
B)
\[(9+5)\hat{\ }(2<4)>2\]
done
clear
C)
\[9+5\div \left( 2<4 \right)\times \text{ }12\]
done
clear
D)
\[9<\text{ }5-2\div \left( 4\text{ }<\text{ }12 \right)\]
done
clear
View Answer play_arrow
If the following words are arranged as found in the dictionary, then what will be the fourth letter from the left in the last word? INTIMATION, INFORMATION, INTEREST, INTERROGATION, INSTIGATION
A)
R
done
clear
B)
0
done
clear
C)
T
done
clear
D)
I
done
clear
View Answer play_arrow
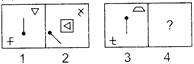
Figures (1) and (2) bear a certain relationship. Similarly, figure (4) bears the same relationship to figure (3). Select the figure from the options which would replace the sign of question mark (?) in Fig. (4).
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
A related pair of figures is given, followed by four answer pairs marked as A, B, C and D. Select that pair which does not have similar relationship as in the given pair.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
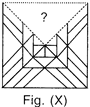
Select the figure from the options which will complete the pattern in Fig. (X).
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
If Nishant is the brother of Brijesh; Mitali is the sister of Nishant; Jai is the brother of Purnima; Purnima is the daughter of Brijesh. Who is the uncle of Jai?
A)
Brijesh
done
clear
B)
Mitali
done
clear
C)
Nishant
done
clear
D)
None of these
done
clear
View Answer play_arrow
In the International games, flags of 6 nations were hoisted in the following way. The flag of America was to the left of Indian Tricolour and to the right of the flag of France. The flag of Australia was on the right of the Indian flag but to the left of the flag of Japan, which was to the left of the flag of China. Find the two flags which are in the center.
A)
America and India
done
clear
B)
Japan and Australia
done
clear
C)
America and Australia
done
clear
D)
India and Australia
done
clear
View Answer play_arrow
Choose the answer which shows the correct water image of the given word.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
How many 6's are there in the series each of which is immediately preceded by 5 but not immediately followed by 9?
A)
4
done
clear
B)
6
done
clear
C)
7
done
clear
D)
5
done
clear
View Answer play_arrow
Which of the following <td> attributes will align contents to the top of the cell in a table in HTML?
A)
valign= "top"
done
clear
B)
align = "top"
done
clear
C)
tdalign = "top"
done
clear
D)
halign = "top"
done
clear
View Answer play_arrow
The
icon in MS-Word 2010 is used to __________.
A)
Create and print envelopes
done
clear
B)
Create and print bookmarks
done
clear
C)
Create and print labels
done
clear
D)
Create and edit the recipient lists
done
clear
View Answer play_arrow
Which of the following options helps you to keep a portion of the sheet visible while the rest of the sheet scrolls in MS-Excel 2010?
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Which of the following features of Windows 7 let you run a program automatically according to the schedule you choose?
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Which of the following levels of data abstraction describes what data are actually stored in the database?
A)
Physical level
done
clear
B)
Conceptual level
done
clear
C)
View level
done
clear
D)
Data level
done
clear
View Answer play_arrow
Which of the following operations does NOT come in the DDL part of SQL?
A)
Creation of table
done
clear
B)
Renaming an object
done
clear
C)
Creation of views
done
clear
D)
Deletion of data
done
clear
View Answer play_arrow
Find the canonical Sum-of-Products form of the given Boolean function. \[F\left( X,Y,Z \right)=\sum{{}}\left( 1,2,5,7 \right)\]
A)
\[xy\overline{z}+\overline{x}\overline{y}\overline{z}+xyz+\overline{x}\overline{z}\]
done
clear
B)
\[xyz+\overline{x}yz+\overline{x}\overline{y}\overline{z}+\overline{x}yz\]
done
clear
C)
\[\overline{x}\overline{y}z+\overline{x}y\overline{z}+x\overline{y}z+xyz\]
done
clear
D)
\[xyz+\overline{x}\overline{y}z+\overline{x}\overline{y}\overline{z}+\overline{x}yz\]
done
clear
View Answer play_arrow
Which of the following protocols is implemented by bridges to build a loop free network topology?
A)
Spanning Tree Protocol
done
clear
B)
Router Information Protocol
done
clear
C)
Telnet
done
clear
D)
User Datagram Protocol
done
clear
View Answer play_arrow
EDGE is a radio based high-speed mobile data standard for transmission. EDGE stands for _________.
A)
External Data for Global Enterprise
done
clear
B)
Extra Data for Global Extranets
done
clear
C)
Enhanced Dynamic Data for Global Enterprise
done
clear
D)
Enhanced Data rates for Global Evolution
done
clear
View Answer play_arrow
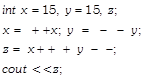
What would be the value of z in the given C++ code?
A)
15
done
clear
B)
20
done
clear
C)
30
done
clear
D)
225
done
clear
View Answer play_arrow
Find the postfix expression for the given infix expression. \[-A+B*C\hat{\ }(D*E)/F\]
A)
\[A-BCDE\hat{\ }*F*/+\]
done
clear
B)
\[A-BCDE*\hat{\ }*F/+\]
done
clear
C)
\[A-BCDE*\hat{\ }*/F+\]
done
clear
D)
\[A-BCDE**/F/\hat{\ }+\]
done
clear
View Answer play_arrow
To delete the selected item permanently without placing the item in the Recycle bin, press _____ in Windows 7.
A)
Shift + Delete
done
clear
B)
Ctrl while dragging an item
done
clear
C)
Ctrl + Shift while dragging an item
done
clear
D)
Alt + Ctrl + Shift
done
clear
View Answer play_arrow
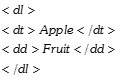
What would be the output of the given HTML code?
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
In _____ transmission, several bits of data are transmitted concurrently through separate communication lines.
A)
Full Duplex
done
clear
B)
Half Duplex
done
clear
C)
Serial
done
clear
D)
Parallel
done
clear
View Answer play_arrow
In relational database, if the elements of a domain are considered to be indivisible units then the domain is called as ____.
A)
Cardinal
done
clear
B)
Dynamic
done
clear
C)
Atomic
done
clear
D)
Virtual
done
clear
View Answer play_arrow
____ option let you find all the names that are used as substitutes for the cell references in MS-Excel 2010.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Look at the diagram and identify the correct rule/theorem.
A)
Associative Rule
done
clear
B)
De Morgan's First Theorem
done
clear
C)
De Morgan's Second Theorem
done
clear
D)
Complementary Rule
done
clear
View Answer play_arrow
Find the minimized form of the following Boolean function. \[F=\overline{x}.\overline{y}.z+\overline{x}.y.z+x.\overline{y}\]
A)
\[x.y+\overline{x}.z\]
done
clear
B)
\[\overline{x}.z+x.\overline{y}\]
done
clear
C)
\[\left( x+y \right).\left( \overline{x}+z \right)~\]
done
clear
D)
\[x.y+z\]
done
clear
View Answer play_arrow
The encryption and decryption algorithms are referred to as ____.
A)
Blowfish
done
clear
B)
Ciphers
done
clear
C)
Private key
done
clear
D)
Ciptext
done
clear
View Answer play_arrow
A process that enables a network to send its data via another network connection is called ____.
A)
Unipolar encoding
done
clear
B)
Symmetric encryption
done
clear
C)
Tunneling
done
clear
D)
Switching
done
clear
View Answer play_arrow
Consider the given SQL table and answer the questions that follow.
What is the cardinality of the given table?
A)
4
done
clear
B)
1
done
clear
C)
3
done
clear
D)
16
done
clear
View Answer play_arrow
Consider the given SQL table and answer the questions that follow.
What would be the output of the given SQL query? \[\begin{array}{*{35}{l}} SELECT\text{ }Salary\text{ }+\text{ }NULL\text{ }FROM\text{ }Employee \\ WHERE\text{ }ID\text{ }=\text{ }432; \\ \end{array}\]
A)
SALARY + NULL
done
clear
B)
NULL
done
clear
C)
0
done
clear
D)
30000
done
clear
View Answer play_arrow
What is WIMM one?
A)
It is a web browser.
done
clear
B)
It is a smart watch.
done
clear
C)
It is a search engine.
done
clear
D)
It is a smartphone.
done
clear
View Answer play_arrow
Which of the following is a layered protocol and Internet standard for transmission of packets over serial lines?
A)
SPP
done
clear
B)
PILP
done
clear
C)
PPP
done
clear
D)
SPS
done
clear
View Answer play_arrow
Find the reduced form of the given Boolean Expression. \[\left( A\text{ }+\text{ }B\text{ }+\text{ }C \right).\text{ }\left( D\text{ }+\text{ }E \right)'\text{ }+\text{ }\left( A\text{ }+\text{ }B\text{ }+\text{ }C \right).\left( D\text{ }+\text{ }E \right)\]
A)
\[D+E\]
done
clear
B)
\[A'\text{ }B'\text{ }C'+AB\]
done
clear
C)
\[A'+\text{ }B'+\text{ }C'+DE\]
done
clear
D)
\[A+B+C\]
done
clear
View Answer play_arrow
____ is the act of posting or sending offensive messages over the internet.?
A)
Plagiarism
done
clear
B)
Spam
done
clear
C)
Flaming
done
clear
D)
Phishing
done
clear
View Answer play_arrow
In SQL, a non-key attribute of a table, which is the primary-key of some other table is known as _____.
A)
Candidate key
done
clear
B)
Alternate key
done
clear
C)
Internal key
done
clear
D)
Foreign key
done
clear
View Answer play_arrow
MAR(Memory Address Register) holds the it
A)
Last instruction
done
clear
B)
Current instruction
done
clear
C)
Location in memory for next read/ write
done
clear
D)
All of these
done
clear
View Answer play_arrow
______viruses are designed to gain administrative control over a system without being detected.
A)
Heuristics
done
clear
B)
Rootkit
done
clear
C)
Real Time
done
clear
D)
Both A and C
done
clear
View Answer play_arrow
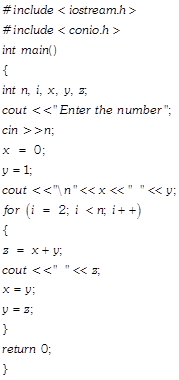
What is this given C++ program used for?
A)
To print the first n terms of the Fibonacci series.
done
clear
B)
To print the factorial of the number.
done
clear
C)
To print the number of digits in a number entered by the user.
done
clear
D)
To check tor Armstrong number.
done
clear
View Answer play_arrow
DNS servers translate web addresses or host names to ____.
A)
Hexadecimal
done
clear
B)
IP address
done
clear
C)
Binary
done
clear
D)
MAC address
done
clear
View Answer play_arrow
____ viruses have characteristics of both Boot sector virus and File infector virus.
A)
Resident
done
clear
B)
Non-Resident
done
clear
C)
Multipartite
done
clear
D)
Real Time
done
clear
View Answer play_arrow
A software which is available free of cost and which allows copying and distribution but not modification is called as ____.
A)
Scare ware
done
clear
B)
Freeware
done
clear
C)
Open Source
done
clear
D)
None of these
done
clear
View Answer play_arrow
Aero shake feature of Windows 7 requires ____ shakes only in order to perform the task.
A)
3
done
clear
B)
2
done
clear
C)
10
done
clear
D)
7
done
clear
View Answer play_arrow
Which of the following is NOT an attribute of \[<tr>\]tag in HTML?
A)
align
done
clear
B)
valign
done
clear
C)
cell padding
done
clear
D)
bg color
done
clear
View Answer play_arrow
What would be the output of the given function in MS-Excel 2010? \[=FLOOR\text{ }\left( 56,\text{ }7 \right)\]
A)
49
done
clear
B)
56
done
clear
C)
50
done
clear
D)
72
done
clear
View Answer play_arrow
Which of the following SQL code is CORRECT, if you want to show the average salary for all the departments with more than 2 people for a job from the table named emp?
A)
Select AVG (sal) from emp GROUP BY deptno HAVING COUNT (empno)\[>2;\]
done
clear
B)
Select AVG (sal) from emp where COUNT>2;
done
clear
C)
Select AVG (sal) from emp GROUP BY (empno) where COUNT \[>2;\]
done
clear
D)
Select AVG (sal) from emp GROUP BY (empno) AND COUNT\[>2;\]
done
clear
View Answer play_arrow
When an individual gains unauthorized OC; access to a computer and tamper with files, this is known as ____.
A)
Software security holes
done
clear
B)
Physical security holes
done
clear
C)
Inconsistent security holes
done
clear
D)
None of these
done
clear
View Answer play_arrow
Identify the given logo, it is a virtual globe, map and geographical information program developed by Google Inc.
A)
Google Globe
done
clear
B)
Google Earth
done
clear
C)
Google Map
done
clear
D)
Google Geo
done
clear
View Answer play_arrow
A class of malware, in which the attacker encrypts the victim's data and demands payment for the decryption key is called _____.
A)
Rescue ware
done
clear
B)
Release ware
done
clear
C)
Ransomware
done
clear
D)
Bribe ware
done
clear
View Answer play_arrow















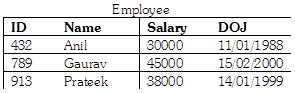 What is the cardinality of the given table?
What is the cardinality of the given table? 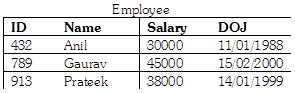 What would be the output of the given SQL query? \[\begin{array}{*{35}{l}} SELECT\text{ }Salary\text{ }+\text{ }NULL\text{ }FROM\text{ }Employee \\ WHERE\text{ }ID\text{ }=\text{ }432; \\ \end{array}\]
What would be the output of the given SQL query? \[\begin{array}{*{35}{l}} SELECT\text{ }Salary\text{ }+\text{ }NULL\text{ }FROM\text{ }Employee \\ WHERE\text{ }ID\text{ }=\text{ }432; \\ \end{array}\]