A cube is coloured red on all of its faces. It is then cut into 64 smaller cubes of equal size. The smaller cubes so obtained are now separated. How many smaller cubes will have at least two surfaces painted with red colour?
A)
4
done
clear
B)
8
done
clear
C)
32
done
clear
D)
24
done
clear
View Answer play_arrow
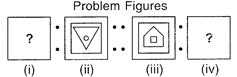
Pair of Problem Figures on either side of has the same relationship. Select the figure from options which will replace "?".
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Pointing to Raman in the photograph, Aditi said, "The only son of his mother is my father". How is Aditi related to Raman?
A)
Mother's sister
done
clear
B)
Father's sister
done
clear
C)
Daughter
done
clear
D)
Niece
done
clear
View Answer play_arrow
In the following letter series, some of the letters are missing. Choose the correct option which complete the series. \[abca\text{ }\_\text{ }bcaab\text{ }\_\text{ }aa\text{ }\_\text{ }caa\text{ }\_\text{ }ca\]
A)
bbac
done
clear
B)
bbaa
done
clear
C)
acbb
done
clear
D)
acac
done
clear
View Answer play_arrow
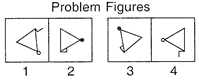
Select the figure to substitute element 4 in the problem figure so that element 3 can be related to element 4 in the same way as element 1 is related to the element 2.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
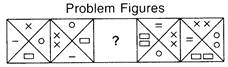
Select the figure which replaces "?", so that the series can be continued in the Problem Figures.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Sunita is taller than Seema and Renu, Renu is shorter than Radha and Gauri, Bina is taller than Radha and shorter than Sunita, Sunita is not the tallest and Renu is not the shortest. Who is the tallest?
A)
Radha
done
clear
B)
Bina
done
clear
C)
Gauri
done
clear
D)
Seema
done
clear
View Answer play_arrow
Find out the missing part that completes the given Fig. (X).
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Find out the missing number.
25 17 41 32 40 11 26 ? 31
A)
26
done
clear
B)
25
done
clear
C)
34
done
clear
D)
38
done
clear
View Answer play_arrow
If \[{{2}^{3}}\div 4=9,{{4}^{4}}\div 8=16,\] then what will be the value of \[{{6}^{2}}\]+4?
A)
9
done
clear
B)
10
done
clear
C)
8
done
clear
D)
12
done
clear
View Answer play_arrow
In C++, when a class contains the objects of another class or its members, it is called_______.
A)
Hiearchialship
done
clear
B)
Membership
done
clear
C)
Containership
done
clear
D)
Partnership
done
clear
View Answer play_arrow
Which of the following cellular technologies is also called as Enhanced GPRS?
A)
GSM
done
clear
B)
CDMA
done
clear
C)
EDGE
done
clear
D)
WLL
done
clear
View Answer play_arrow
Which of the following is a LAN spreading worm for OS X systems that cannot spread over the internet?
A)
Mellisa
done
clear
B)
Morris
done
clear
C)
Zombie
done
clear
D)
Oompa-Loompa
done
clear
View Answer play_arrow
A portion or part of WWW content that is not indexed by standard search engines is called _______.
A)
Surface Web
done
clear
B)
Deep Web
done
clear
C)
Bright Web
done
clear
D)
Light Web
done
clear
View Answer play_arrow
Which of the following is NOT an input type in HTML?
A)
Text
done
clear
B)
Radio
done
clear
C)
Password
done
clear
D)
Fixed
done
clear
View Answer play_arrow
______option will allow you to create an AutoText entry in MS-Word 2010.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
______ tag in HTML is used to apply formatting style to one or more columns in a table.
A)
\[<columngroup>\]
done
clear
B)
\[<group>\]
done
clear
C)
\[<colgroup>\]
done
clear
D)
\[<combine\text{ }cols>\]
done
clear
View Answer play_arrow
Which of the following is a remote controlling feature in Windows 7 that allows a user to control a remote window computer over a network or the internet?
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
The output of the given function in MS-Excel 2010 is _______. \[=FIND\left( ''li'',''discipline'',3 \right)\]
A)
4
done
clear
B)
3
done
clear
C)
7
done
clear
D)
10
done
clear
View Answer play_arrow
\[~X\text{ }\left( Y\text{ }+\text{ }Z \right)\text{ }=\text{ }XY\text{ }+\text{ }XZ\]is the _____ law in Boolean Algebra.
A)
Associative
done
clear
B)
Distributive
done
clear
C)
Involution
done
clear
D)
Commutative
done
clear
View Answer play_arrow
Which of the following HTML tags will not eliminate extra white space or line breaks and display the text in the browser exactly as it is written in HTML document?
A)
\[<default>\]
done
clear
B)
\[<pre>\]
done
clear
C)
\[<cite>\]
done
clear
D)
done
clear
View Answer play_arrow
Which of the following benefits is/are offered by Home Group Networking feature in Windows 7?
A)
Easy sharing of libraries and other files throughout the Home Group in Windows Explorer.
done
clear
B)
Easy access to shared media libraries in Windows Media Player and Windows Media Center.
done
clear
C)
Ability to stream media to devices (other computers, media extenders and players, digital picture frames, and so on) using Play To.
done
clear
D)
All of these
done
clear
View Answer play_arrow
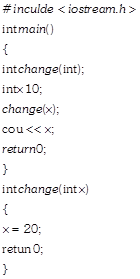
What will be the value of x in the given C++ program?
A)
10
done
clear
B)
30
done
clear
C)
20
done
clear
D)
No output
done
clear
View Answer play_arrow
Which of the following header files will be required to be included for the following built-in functions in C++? \[isupper(),\text{ }isalnum()\]
A)
\[<math.h>\]
done
clear
B)
\[<ctype.h>\]
done
clear
C)
\[<string.h>\]
done
clear
D)
\[<iomanip.h>\]
done
clear
View Answer play_arrow
Which of the following apps uses natural language user interface and speech recognition technologies to accomplish its tasks?
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Select the INCORRECT SQL query.
A)
DELETE FROM students WHERE age \[>\] 20;
done
clear
B)
DELETE FROM students WHERE 75 = Percent;
done
clear
C)
UPDATE Class SET Section = 'A';
done
clear
D)
INSERT INTO items (Item Value, Item Name) values (2101, 'Pencil');
done
clear
View Answer play_arrow
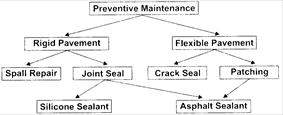
In the given database model the schema is viewed as a graph rather than the tree of records. Identify it.
A)
Hierarchical model
done
clear
B)
Relational model
done
clear
C)
Network model
done
clear
D)
Object model
done
clear
View Answer play_arrow
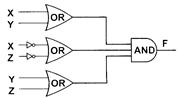
Find the CORRECT Boolean Expression for the given logic circuit diagram.
A)
\[F\left( X,Y,Z \right)=\left( X.Y \right)+\left( X.\overline{Z} \right)+\left( \overline{Y}.\left( \overline{X}.Z \right) \right)\]
done
clear
B)
\[F\left( X,Y,Z \right)=\left( X+Y \right).\left( \overline{X}+\overline{Z} \right).\left( Y+Z \right)\]
done
clear
C)
\[F\left( X,Y,Z \right)=\left( X+Z \right).\left( \overline{X}+Z \right).\left( Y+Z \right)\]
done
clear
D)
\[F\left( X,\text{ }Y,\text{ }Z \right)=\left( X+\text{ }Y \right).\left( X+\text{ }Z \right).\left( Y+\text{ }Z \right)\]
done
clear
View Answer play_arrow
Select the CORRECT dual for the given Boolean Expression. \[ABC\text{ }+\text{ }A\overline{B}C\text{ }+\text{ }\overline{A}B\overline{C}\]
A)
\[(A.1)+(A+0.\overline{A})\]
done
clear
B)
\[\left( A+B \right).\left( \overline{A}+B \right).\left( \overline{B}+\overline{C} \right)\]
done
clear
C)
\[\left( A+B+C \right).\left( A+\overline{B}+C \right).\left( \overline{A}+B+\overline{C} \right)\]
done
clear
D)
\[AB\text{ }+\text{ }\overline{A}B\text{ }+\text{ }\left( A.B.C \right)\]
done
clear
View Answer play_arrow
MAC is a short piece of information that protects both a message's data integrity as well as its authenticity. Here, MAC stands for __________.
A)
Message Authentication Code
done
clear
B)
Message Authentication Cryptography
done
clear
C)
Message Authentication Computation
done
clear
D)
Message Authentication Channel
done
clear
View Answer play_arrow
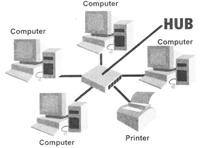
Identify the type of topology shown in the given diagram.
A)
Star topology
done
clear
B)
Bus topology
done
clear
C)
Tree topology
done
clear
D)
Graph topology
done
clear
View Answer play_arrow
A device that electrically amplifies the signal as it moves from one connected device to another is called ____.
A)
Exo Hub
done
clear
B)
Active Hub
done
clear
C)
Passive Hub
done
clear
D)
Bridge
done
clear
View Answer play_arrow
Which of the following options is used to delete the duplicate entry from the selected cell range in MS-Excel 2010?
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
______ encryption uses one secret key provided to both the parties in cryptography technique.
A)
Symmetric
done
clear
B)
Asymmetric
done
clear
C)
Extended
done
clear
D)
Dynamic
done
clear
View Answer play_arrow
Identify the following:
- It is a computer program that replicates itself. - It includes a code called payload to delete the files. - Morris and Code Red are its examples.
A)
Virus
done
clear
B)
Worm
done
clear
C)
Trojan
done
clear
D)
Brain
done
clear
View Answer play_arrow
Which of the following is/are the requisites for a software for being an open source?
A)
Derived works must be allowed.
done
clear
B)
No discrimination among persons or groups.
done
clear
C)
License must not be specific to a product.
done
clear
D)
All of these
done
clear
View Answer play_arrow
____ is a computer software used to refer both open-source and free softwares.
A)
OSS
done
clear
B)
FOSS
done
clear
C)
FSF
done
clear
D)
GNU
done
clear
View Answer play_arrow
In C++, if "A" is a character pointer, then the expression A++ will increment the pointer by ____ byte/bytes.
A)
2
done
clear
B)
4
done
clear
C)
8
done
clear
D)
1
done
clear
View Answer play_arrow
Which of the following statements holds true in context of MS-Word 2010?
Statement 1: Footnotes are numbered manually by the user. Statement 2: You can track only the insertion changes.
A)
Only Statement 1
done
clear
B)
Only Statement 2
done
clear
C)
Neither Statement 1 nor Statement 2
done
clear
D)
Both Statement 1 and Statement 2
done
clear
View Answer play_arrow
Select the odd one out.
A)
done
clear
B)
done
clear
C)
done
clear
D)
done
clear
View Answer play_arrow
Identify the following:
- It is the network of physical objects embedded with electronics, software and sensors that involves machine to machine communication (M2M) without any human interaction. - Its examples are heart monitoring implants and automobiles with built, in sensors.
A)
Information of Objects
done
clear
B)
Internet of Things
done
clear
C)
Cloud Computing
done
clear
D)
Internet Harvesting
done
clear
View Answer play_arrow
_____ is a computer worm affecting Microsoft Windows. It is also known as Novarg.
A)
Trojan
done
clear
B)
My doom
done
clear
C)
Brain
done
clear
D)
Boot sector
done
clear
View Answer play_arrow
Which of the following columns can be omitted in an INSERT statement in SQL?
A)
Having default value defined.
done
clear
B)
Allowing NULL values.
done
clear
C)
Can't omit any column value
done
clear
D)
Both A and B
done
clear
View Answer play_arrow
Which of the following is considered a the first Macro virus, that attacked Microsoft Word documents?
A)
SQL Injection
done
clear
B)
CIH
done
clear
C)
Concept
done
clear
D)
Dendroid
done
clear
View Answer play_arrow
____is a client/server software program that allows multiple users to communicate online with real-time audio, video and text chat in dynamic 3D environments.
A)
Network
done
clear
B)
Newsgroup
done
clear
C)
Interspace
done
clear
D)
Metropolitan Area Network
done
clear
View Answer play_arrow
Find the postfix form of the following infix expression. \[A+\left[ \left( B\text{ }+\text{ }C \right)+\left( D\text{ }+\text{ }E \right)*F \right]/G\]
A)
\[ABC+DEF+*+G/+\]
done
clear
B)
\[ABC+\text{ }D+\text{ }E+\text{ }F*+\text{ }G/\]
done
clear
C)
\[AB+\text{ }CD+\text{ }EF*+\text{ }G/+\]
done
clear
D)
\[ABC+\text{ }DE\text{ }+\text{ }F*+\text{ }G/+\]
done
clear
View Answer play_arrow
Which of the following LAN network does NOT require a Network Interface Card?
A)
Dedicated Server
done
clear
B)
Peer-to-Peer
done
clear
C)
Zero-Slot
done
clear
D)
None of these
done
clear
View Answer play_arrow
Which of the following SQL commands is CORRECT, if you want to display name and section of those students whose section is either A or C?
A)
SELECT name, section FROM students WHERE section BETWEEN ('A', 'C');
done
clear
B)
SELECT name, section FROM student WHERE section LIKE 'A' and 'C';
done
clear
C)
SELECT name, section FROM student WHERE section IN ('A', 'C');
done
clear
D)
SELECT name, section FROM students WHERE section BETWEEN 'A' AND 'C';
done
clear
View Answer play_arrow
Which of the following best describes Jabber?
A)
An error that states that a static IP address is used by some outer device on the network.
done
clear
B)
A social networking site.
done
clear
C)
A device to broadcast the same message to multiple LAN segments.
done
clear
D)
An error in which a faulty device continuously transmits corrupted data onto a network.
done
clear
View Answer play_arrow
An open-source Network Intrusion Prevention System (NIPS) that performs real-time traffic analysis and packet logging on IP network is called______.
A)
Snort
done
clear
B)
Snarf
done
clear
C)
Snobby
done
clear
D)
Speedy
done
clear
View Answer play_arrow